🛡️ How to enable Azure AD Security Defaults in Microsoft 365?
What is Azure AD Security Defaults
Azure AD Security Defaults is a security feature in Azure Active Directory (Azure AD) that automatically enables recommended security settings for new tenants in Azure AD. These settings are designed to tenant increase security and to protect users from known security threats.
Azure AD Security Defaults includes:
- Mandatory password policy: a policy that requires passwords to be complex, unique and changed regularly.
- Multi-factor authentication(MFA): a layer of security that requires users to confirm their identity using multiple methods, such as a code sent via SMS or a fingerprint reader.
- Protection against brute force attacks: a security measure that causes a temporary block to be placed on the account after a certain number of failed login attempts.
Azure AD Security Defaults is enabled by default for new tenants and cannot be disabled. As an administrator, if you want to adjust settings or enable additional security features, you can manage security features in Azure AD .
In this article, you can read how to enable Azure AD Security Defaults at the bottom.
1. Registration of Multi-Factor Authentication.
All users in your Tenant will need to register for multi-factor Authentication (MFA)
Users have 14 days to register for Multi-Factor Authentication using the Microsoft Authenticator app.
After these 14 days, the user must log in with MFA only after registration is complete.
2. Enforce Multi-Factor Authentication for all users.
Secure administrators
After the above registration with Multi-Factor Authentication is complete , the following 9 Azure AD administrators will need to perform additional authentication every time they log in. (default behavior)
- Global administrator
- SharePoint-administrator
- Exchange-administrator
- Administrator of conditional access
- Security Administrator
- Help desk administrator or password administrator
- Billing Administrator
- User administrator
- Verification administrator
3. Secure all users with MFA
We tend to think that administrator accounts are the only accounts that need extra layers of security. Administrators have tremendous access to sensitive information and can make changes to settings for the entire organization.
When these hackers gain access, they can claim access to the organization on behalf of the holder of the original account. They can download the entire directory to launch a phishing attack on your entire organization. (phishing mail)
A common method for improving security for all users is to require a stronger form of account authentication. MFA.
4. Blocking legacy authentication.
Older Office clients that cannot use modern authentication (for example, an Office 2010 client).
Any client that uses older e-mail protocols, such as IMAP, SMTP or POP3.
What is pop3? POP3(Post Office Protocol) is a protocol to retrieve mail thanks to an e-mail program such as Microsoft Outlook. With POP3, you always have your Inbox on your own PC. Upon retrieval, all incoming e-mail messages are deleted.
What is IMAP? You can configure IMAP on any computer without having mails "pulled in" to the e-mail client. Imap is a protocol that is often applications in use. Ordinary Office 365 users do not need POP3 or IMAP.
Most attempts to log on, with with outdated authentication. Outdated authentication does not support Multi-Factor Authentication.
After the default security settings are enabled in your Tenant, all authentication requests performed by an older protocol are blocked. Default security settings do not block ExchangeActiveSync. But perhaps you also use the Outlook application. https://365tips.be / ?p=289
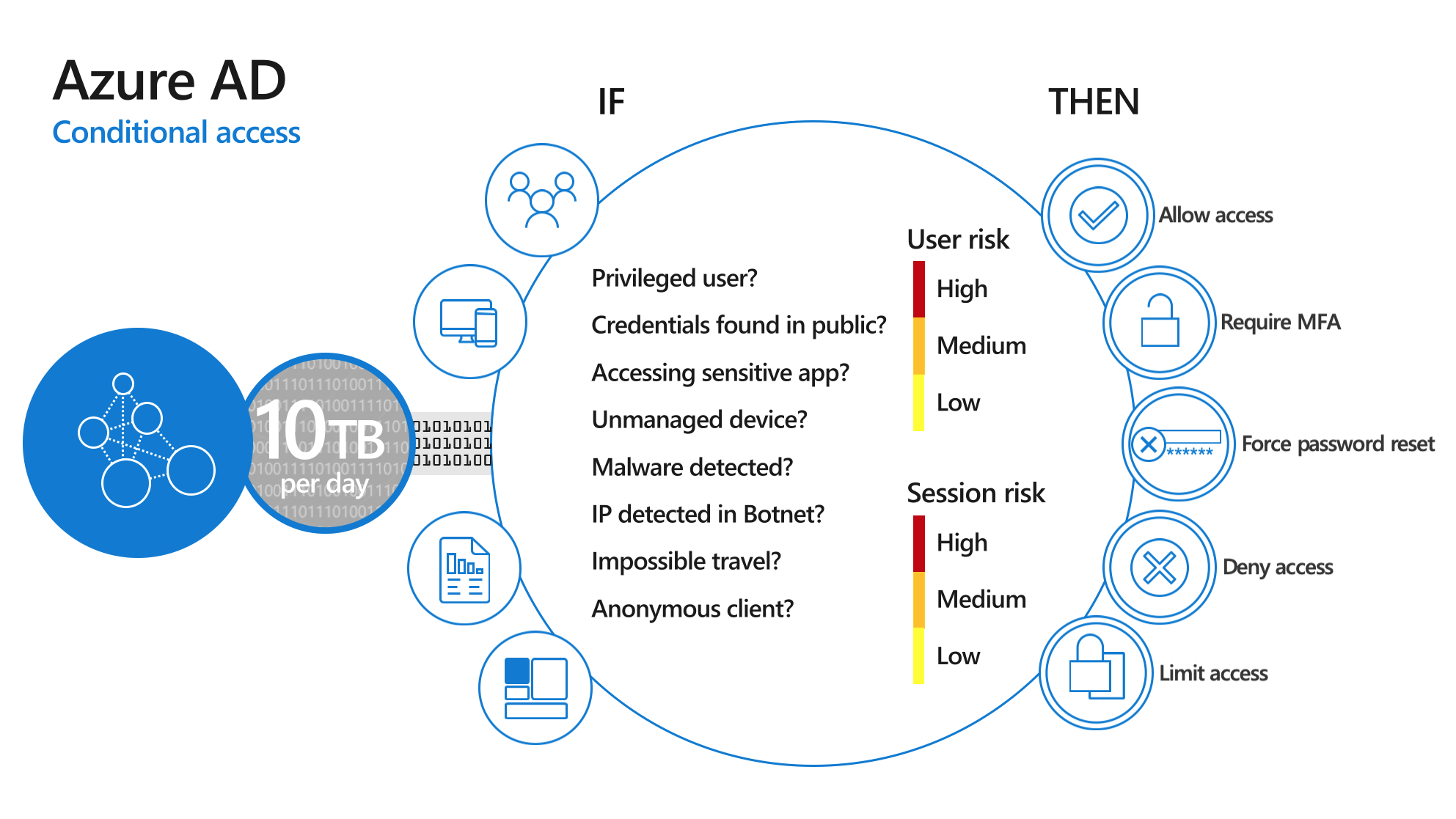
5. Conditional access
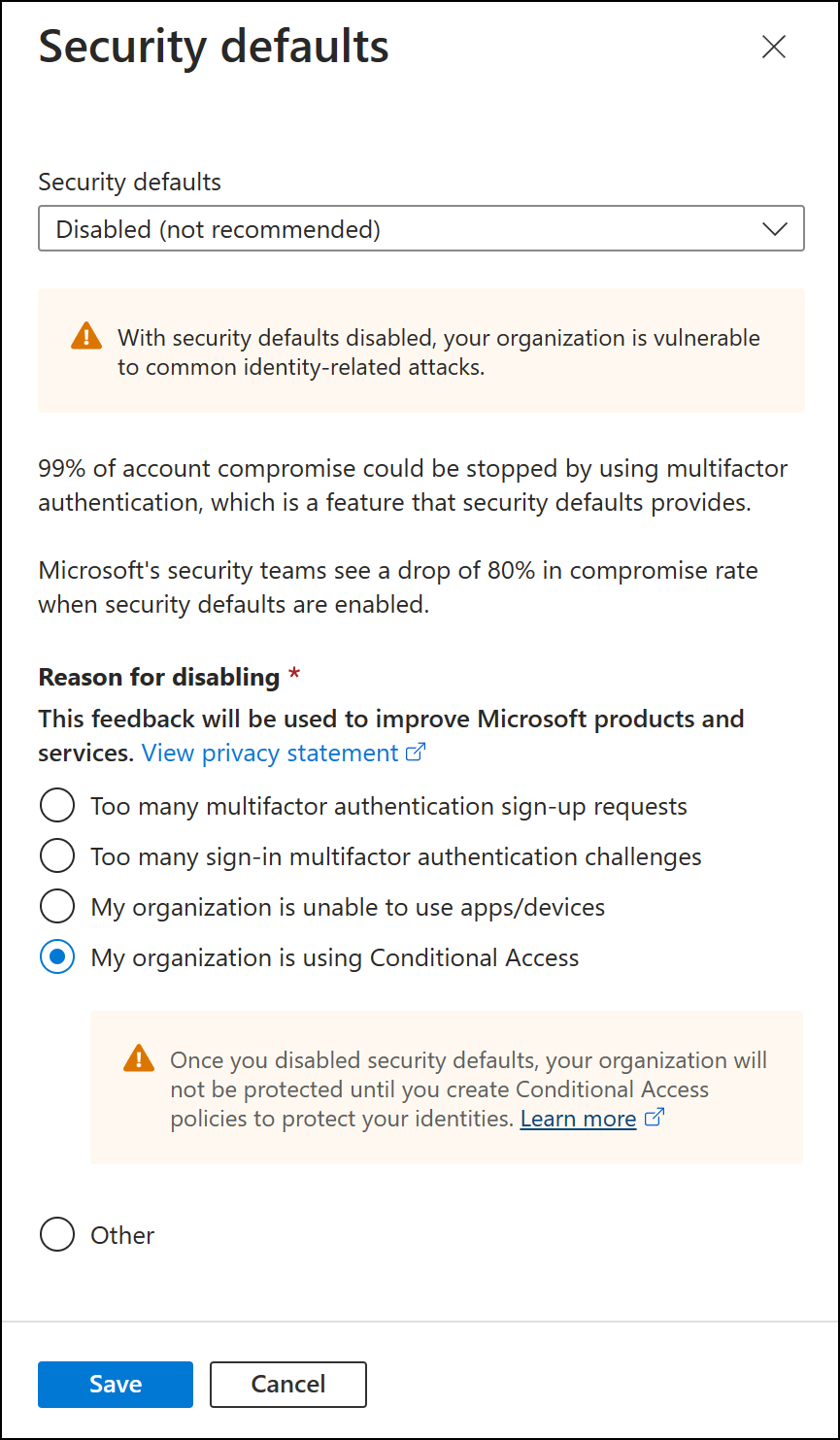
You can also start your own conditional access on groups and user roles. Then it's best not to choose this configuration.
If you want to do it yourself, you can 't use the defaults and you have to disable it.
Conditional access = Giving access to a service on conditions. IF="Unmanaged device"
THEN="Require MFA"
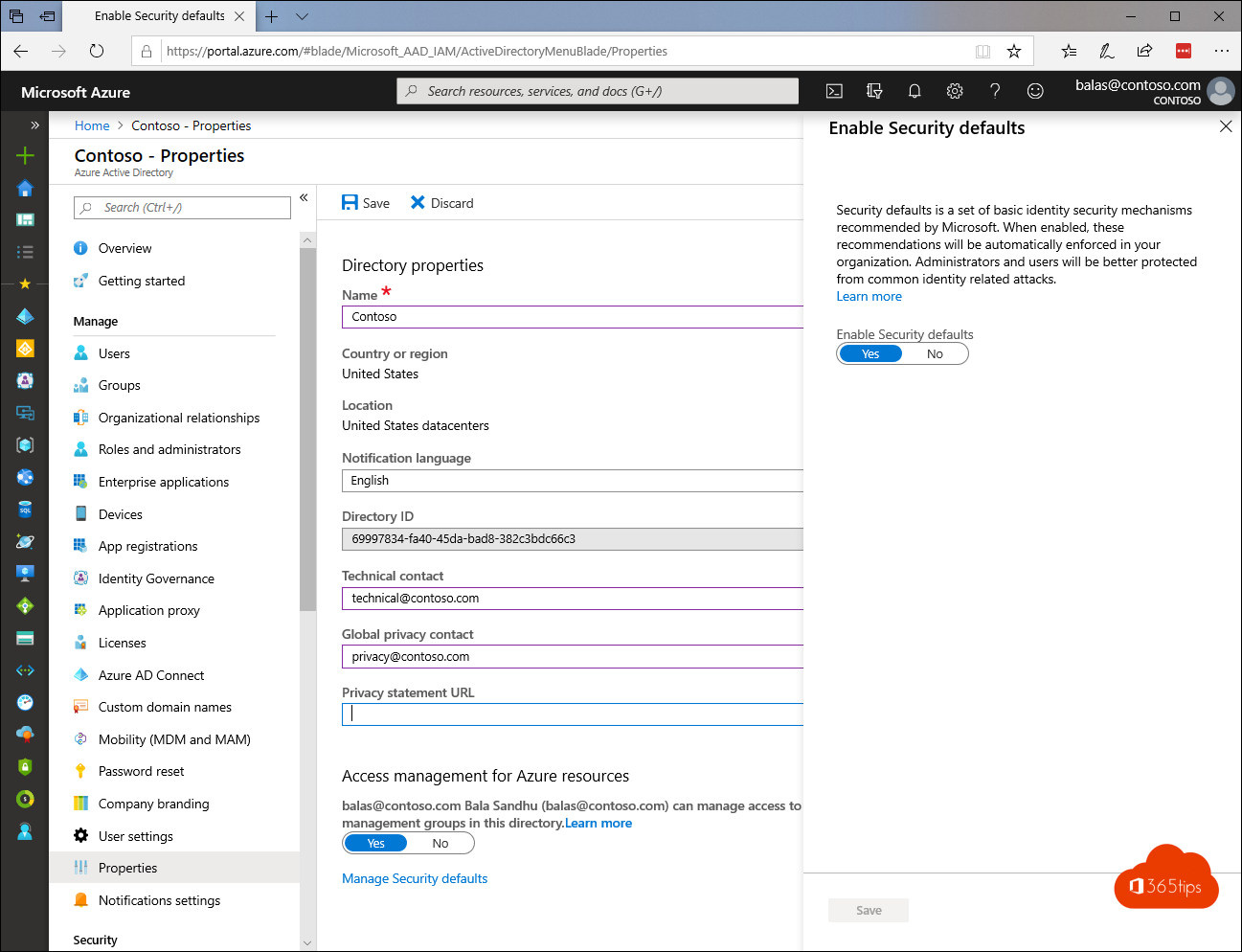
6. How to enable this Azure AD Security default?
Enable default settings for security in your Directory:
Log in to theAzure Portal as a security administrator, conditional access administrator or global administrator. -> Enable Security defaults - Microsoft Azure
Navigate to -> Azure Active Directory -> properties.
Select Manage default security settings.
Set the Enable default settings option to Yes.
Select Save.