Office 365 set alert policy
A good document management policy for Microsoft 365 should regulate every service within Microsoft. Some organizations choose to disable external sharing on OneDrive, SharePoint and Teams. But often leave the door open for other creative solutions. Here are some examples and solutions to address this challenge.
Office 365 design
To cover everything, it's best to also set up each Office 365 service properly. In these 3 previous blogs, I went into more detail on: Microsoft Teams, OneDrive For Business and SharePoint Online.
How do office 365 policies work?
Policies are set by administrators. Users do actions that will trigger the policy-> an alert will be created and sent to specific people within the organization. Such as the DPO or CISO.
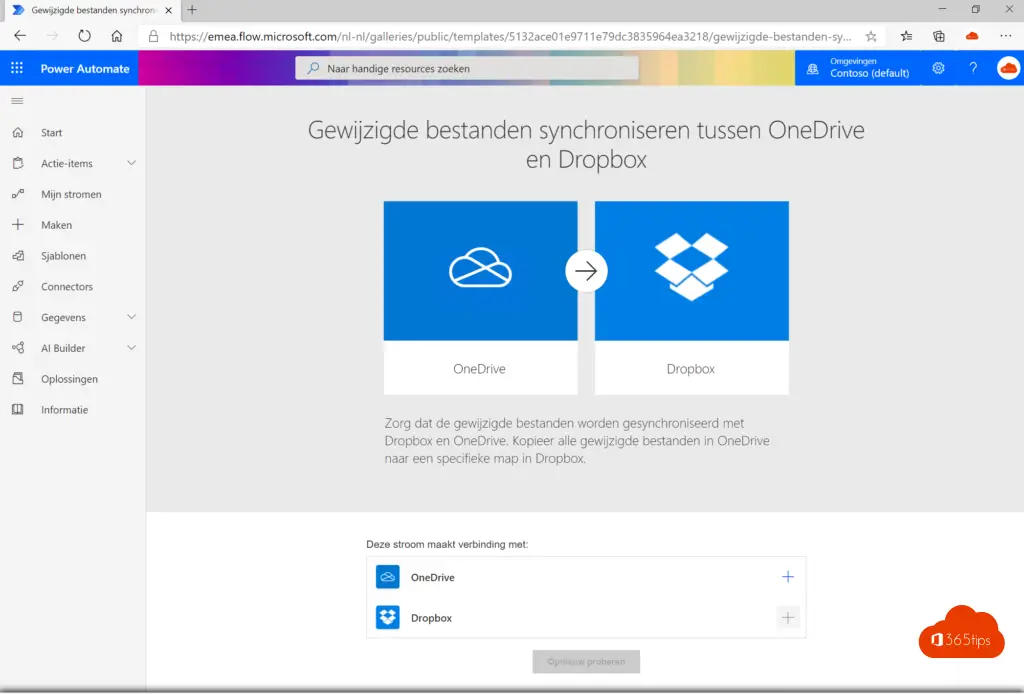
Microsoft Flow
If you don't want to allow sharing of documents outside Teams, SharePoint & OneDrive, Microsoft Flow is a challenge. Information protection labels allow you to label files when a document will be shared that should not be opened by the recipient. This is the best placed solution to address the full document challenge.
SharePoint Online
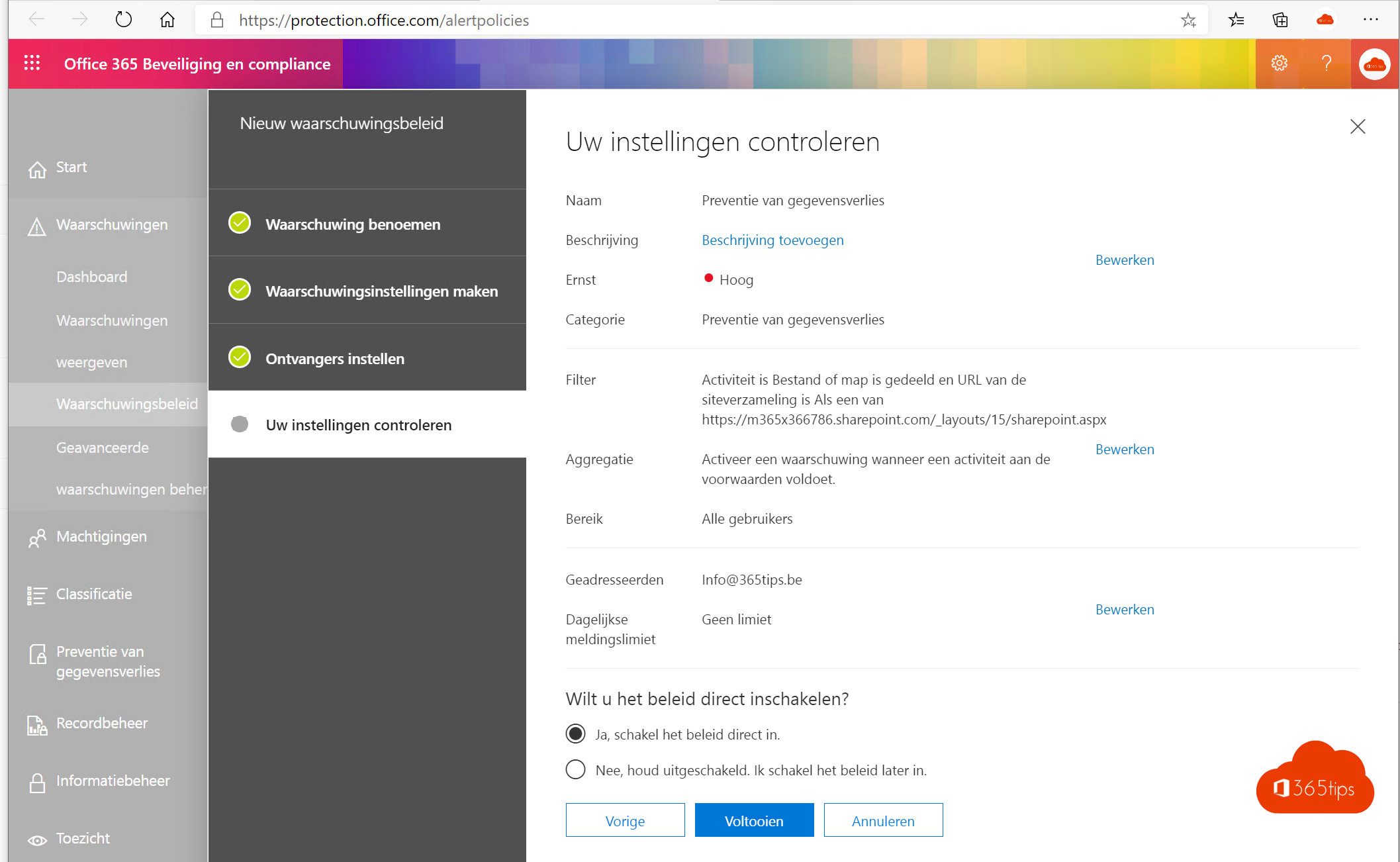
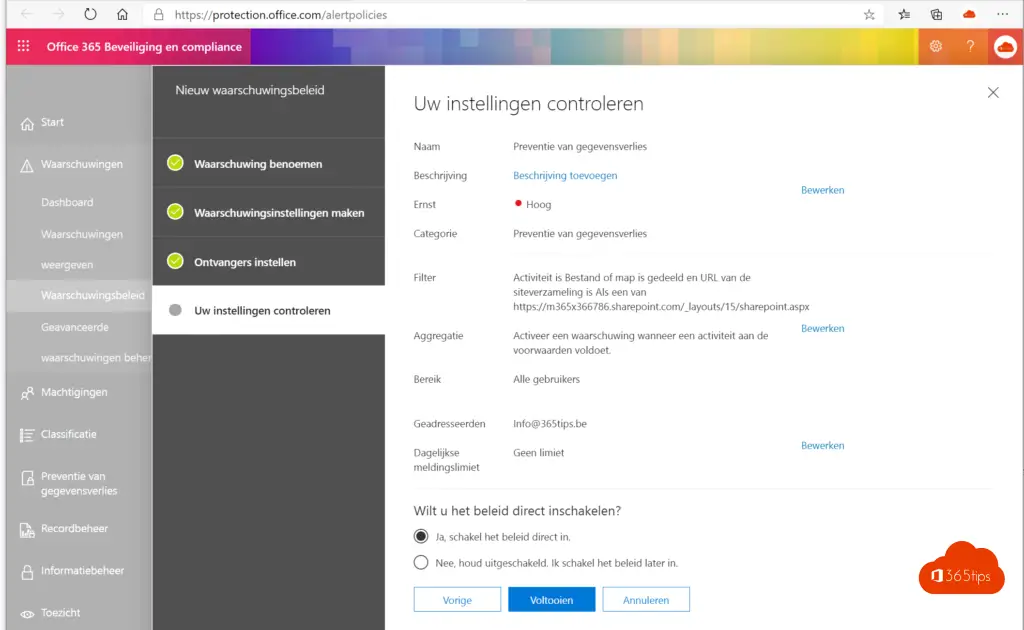
Within SharePoint online it is possible to provide notifications when users share folders or files so that you can be reactive. These notifications can be set via: https://protection.office.com/alertpolicies in addition, it is also possible to apply Information Protection and intercept files based on a classification when leaving the organization.
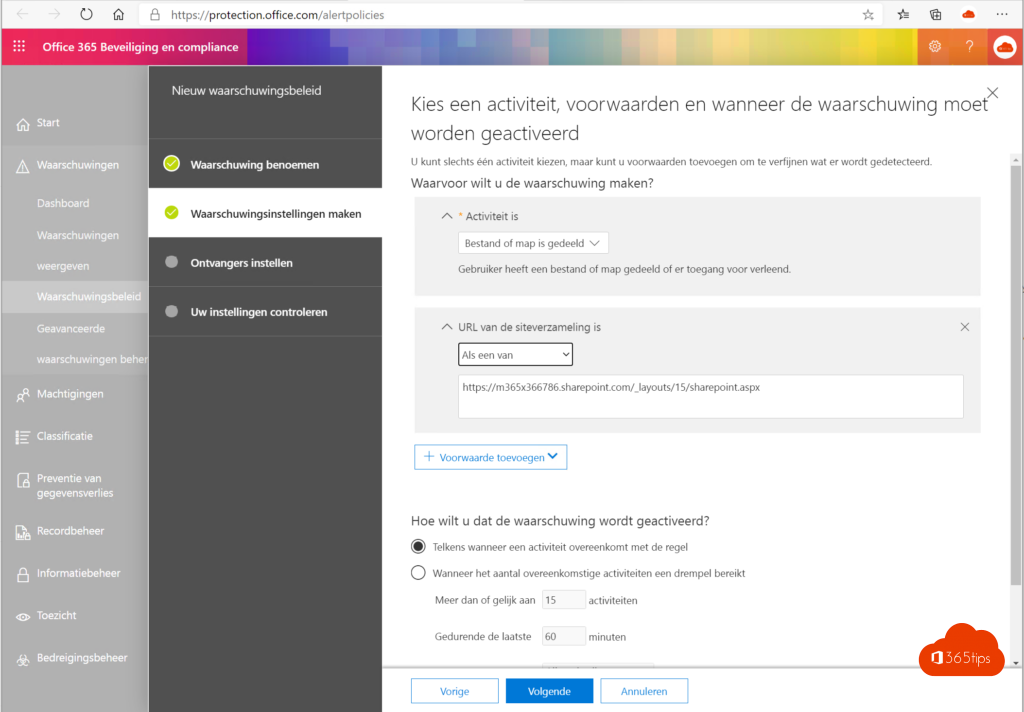
In this example, a policy was set that ensures the adminstrator receives an email when someone shares a file from within the organization at SharePoint.
Enabling information protection
Information protection gives the ability to label and classify documents at the file level so that if they will be leaked they will not be readable by the recipients. Unless those recipients were given explicit access.
Enabling information protecion can be done through this blog. In one of the following blogs you will read a hands-on guide to intercept files in the movement so that they cannot leave the organization.
