How can you automatically change your office 365 password in the event of a risk or hack?
Microsoft has a solution to automatically change the password if it appears on a hacked list, or an attempt that does not come from the user.
Through Cloud AI, Microsoft learns if it is okay for users to log in from their location or device. This combined with other data points gives the ability to predict whether the user is the "real deal."
Activation of user risk policy in Office 365
To ensure that the compromised accounts of high-risk users are forced to perform a password change at login, you can implement a user risk policy.
If you do not have an MFA, you cannot make your users change their passwords. They will only be blocked, unfortunately. And a sign-in risk will appear in Azure Active Directory.
It is an added value for users to activate MFA because they are able to change their password themselves in case of a risk. Where before they had to contact their IT department.
A policy will also need to be created to make these settings active after activation. Useful here is that IT admins can also use these "conditions" on other identity-based Azure AD integrations.
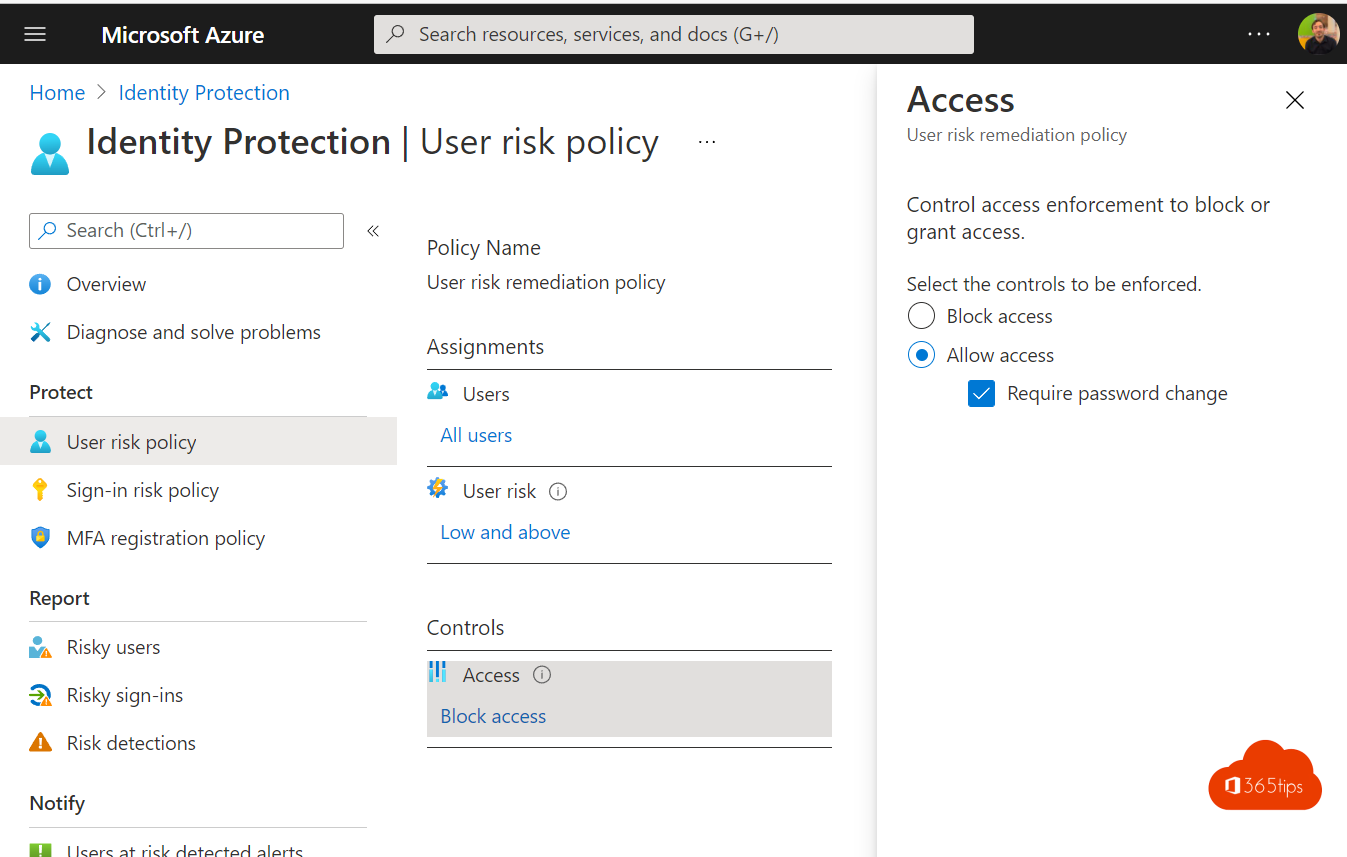
Technical activation to perform a password reset in Microsoft 365
To activate the policy, please follow the instructions below
Browse to: IdentityProtectionMenuBlade/UserPolicy
Create a policy for user risks
Click on all users.
User risks: Medium or High.
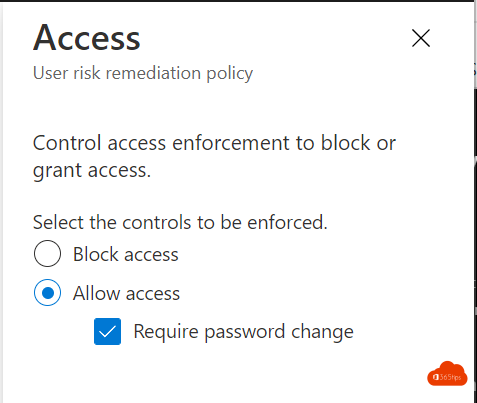
Enforce policies ON.
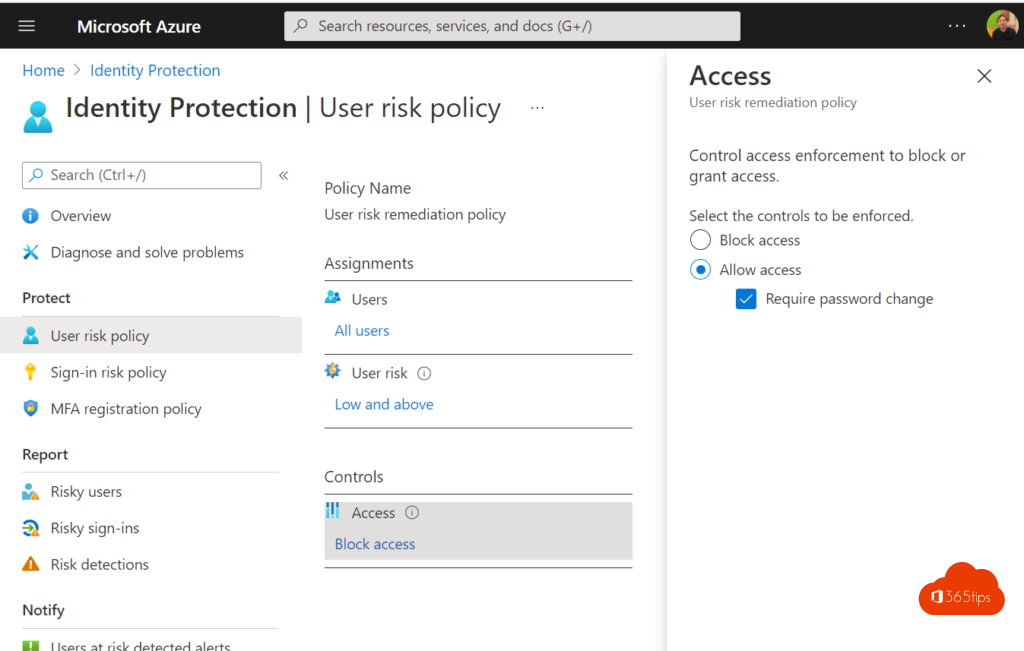
- Remember to turn password change requirements ON.
What licenses do you need to activate additional security measures
Microsoft 365 E5, Microsoft 365 E3 or Microsoft 365 Business Premium. Build out your workplace and activate multiple services to justify the upgrade and take full advantage of the added value. For just this feature, it may not be appropriate to cover the additional cost.
Also read
Microsoft Security: How to use Office 365 Advanced Threat Protection advisor?
Configure Azure Advanced Threat protection and Cloud App Security Protection
Make your organization more secure with a single click thanks to Azure AD Security Defaults