Use Azure AD to understand Risky Sign-ins in Microsoft 365 and Azure AD
It is important for organizations to consider implementing multi-factor authentication(MFA), especially if they are not yet able to deploy this security measure. Using MFA can help reduce the risk of user accounts being misused by attackers who have access to passwords. MFA is one of the most recommended security features to implement because it adds an extra layer of security by requiring users to provide second factor verification before accessing certain systems or data. If you want to know how to activate MFA in Microsoft Office 365, you can follow the steps described in this link.
How Azure AD activate risky sign-ins with a demo account
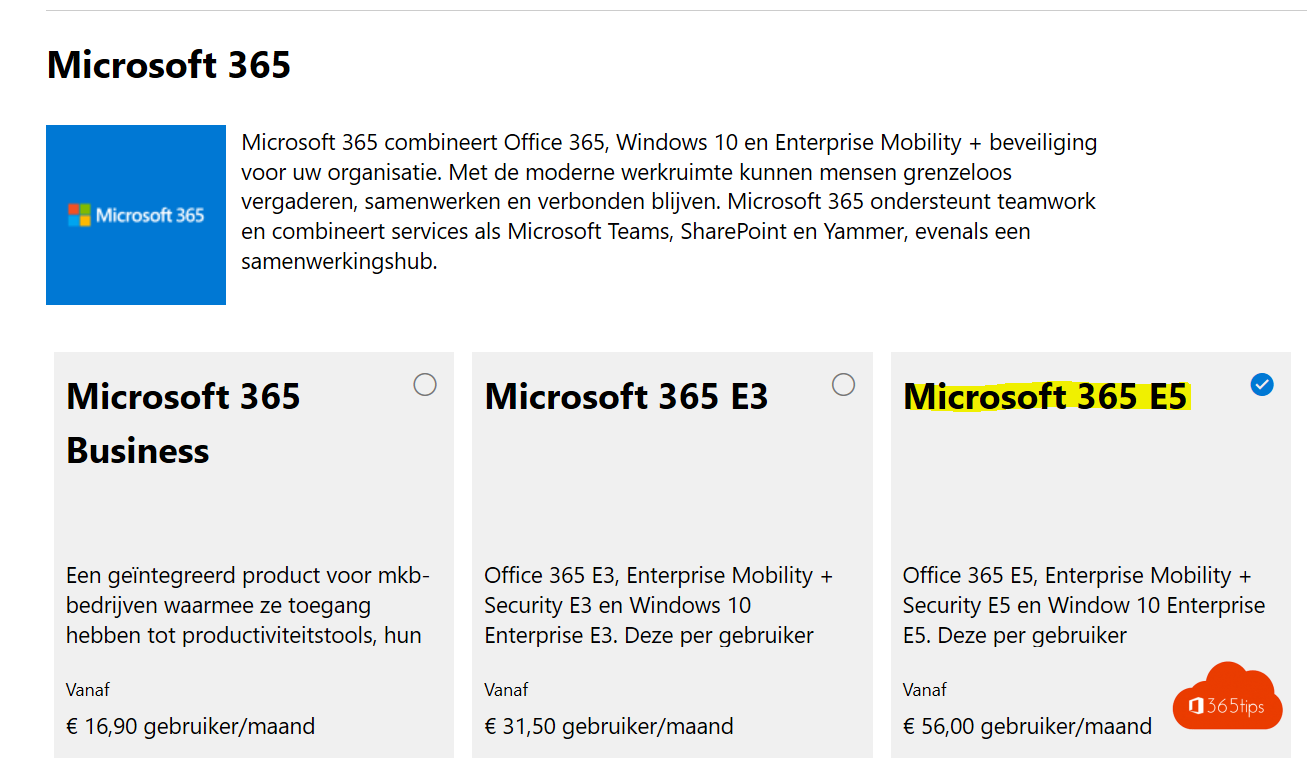
Activate a demo license of Microsoft 365 E5 via admin.microsoft.com and activate it on your user account.
Thanks to Azure AD Microsoft 365, you are able to pull reports of Risky sign-ins, Risky users, etc.
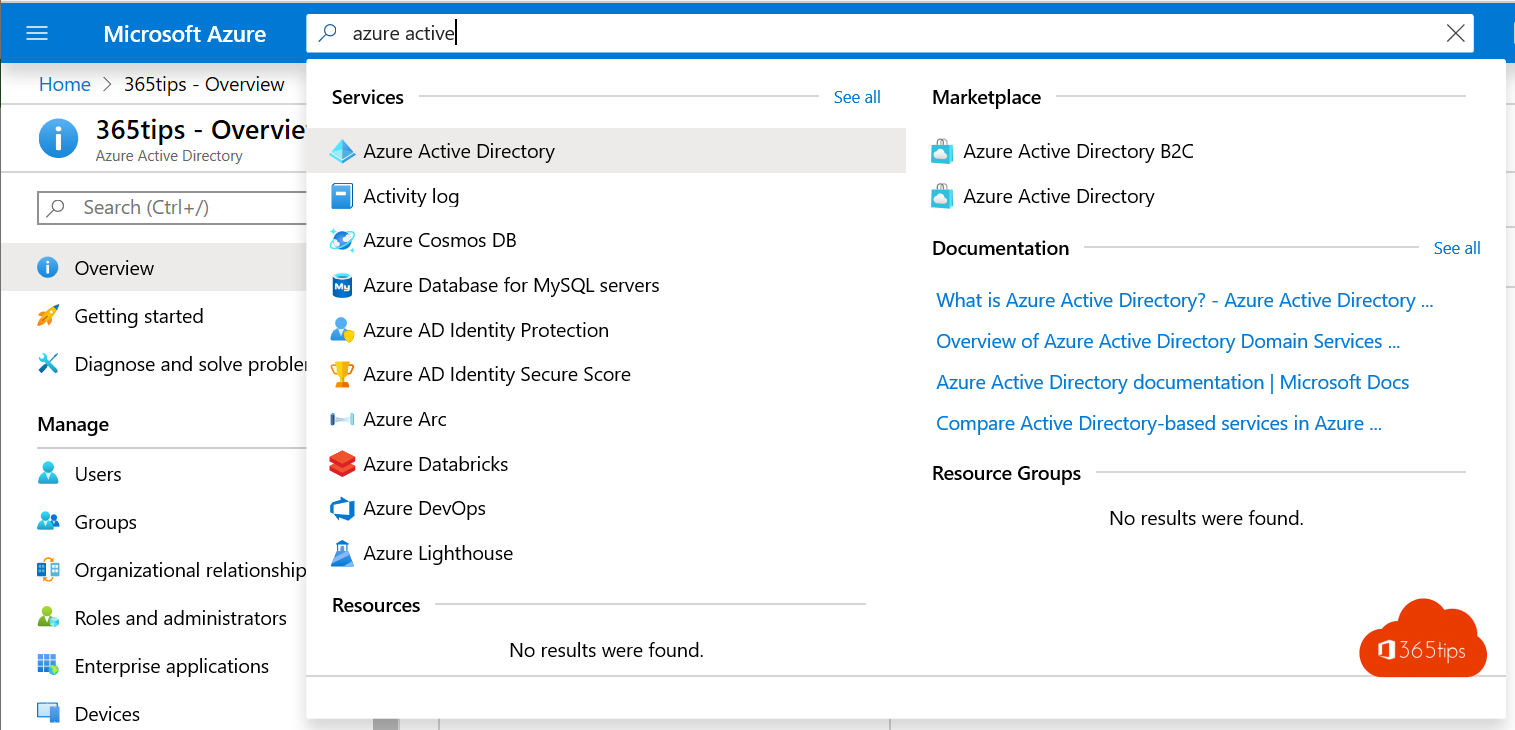
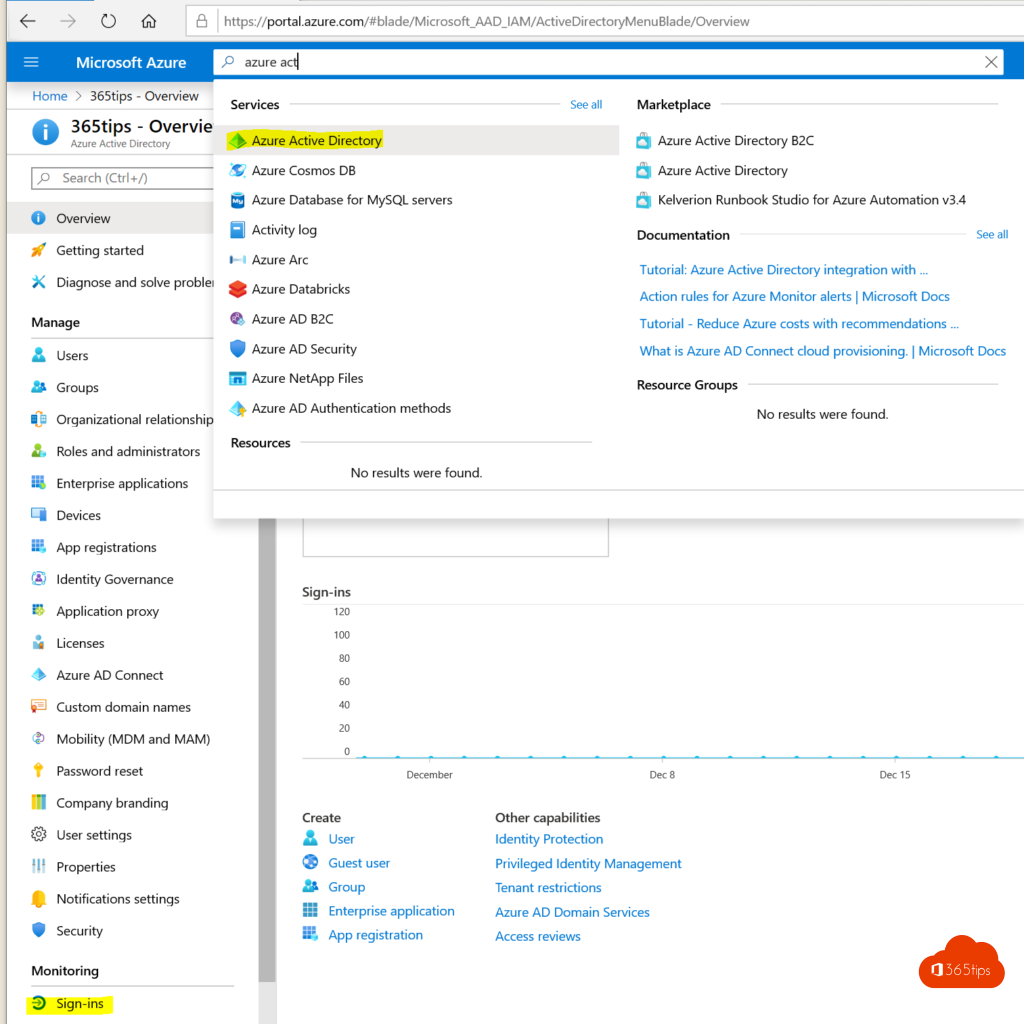
Browse to https://po rtal.azure.com.
Open Azure Active Directory -> Open report: Here you will see Risky Users, Risky Sign-ins and Risk Detection.
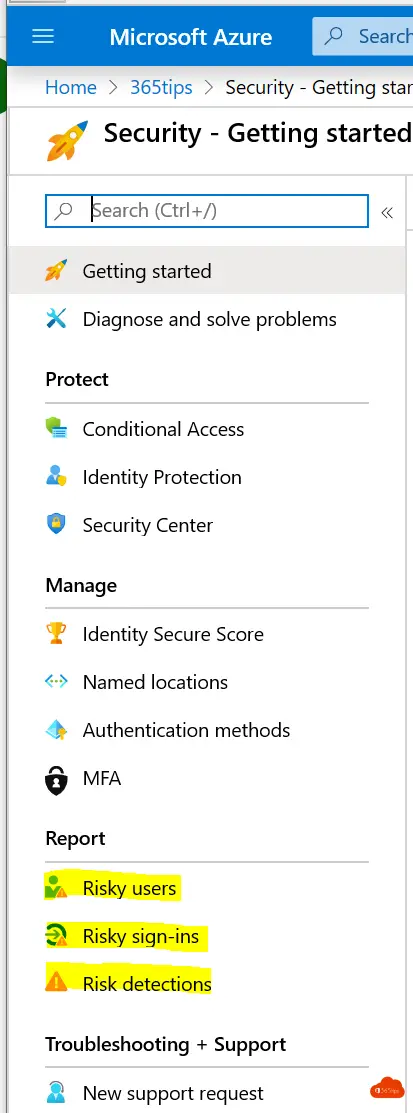
In this report, you can see all the risks on all current users.
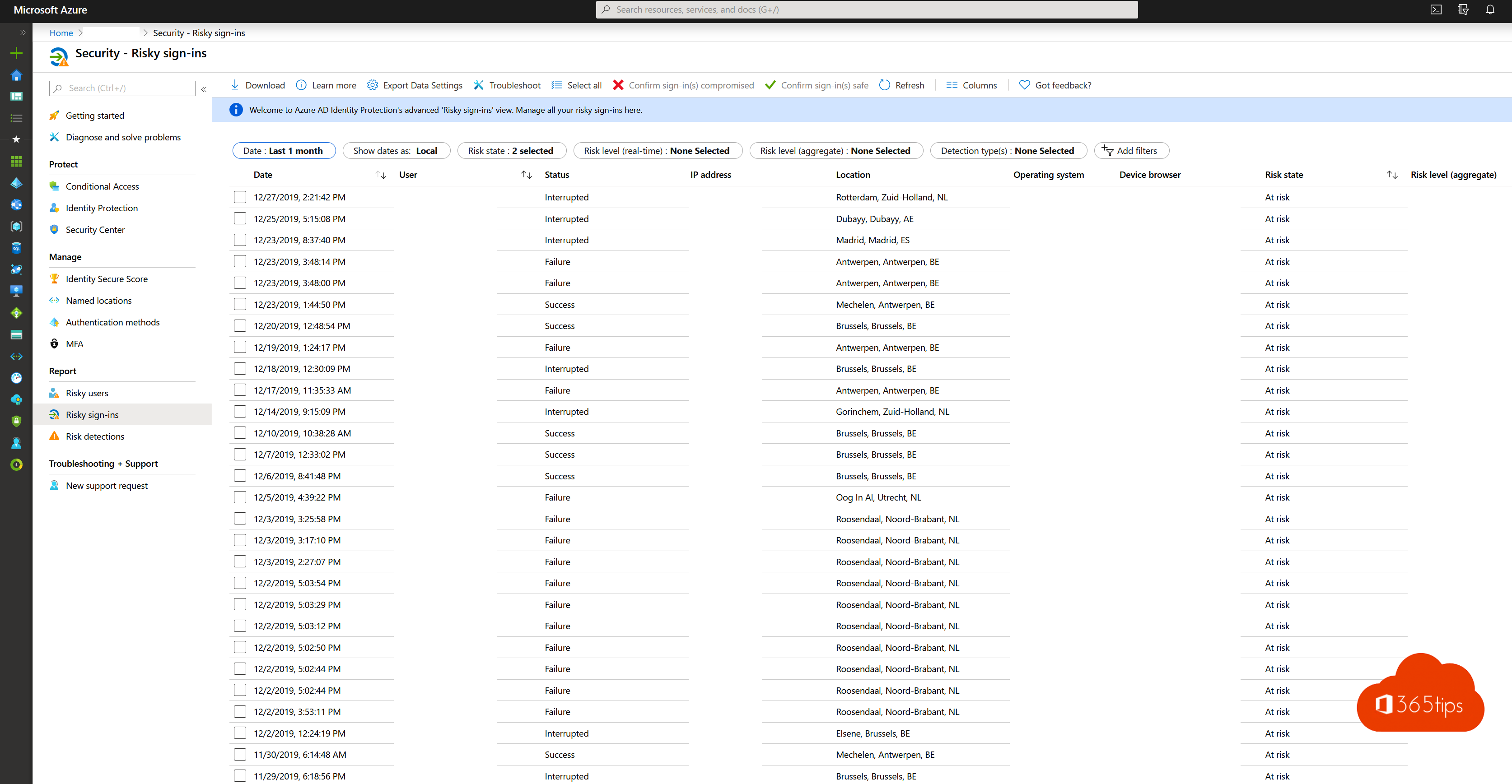
If you select the user you can see why they have increased risks.
Azure AD Use exports to create an analysis in CSV format
Open Azure Active Directory.
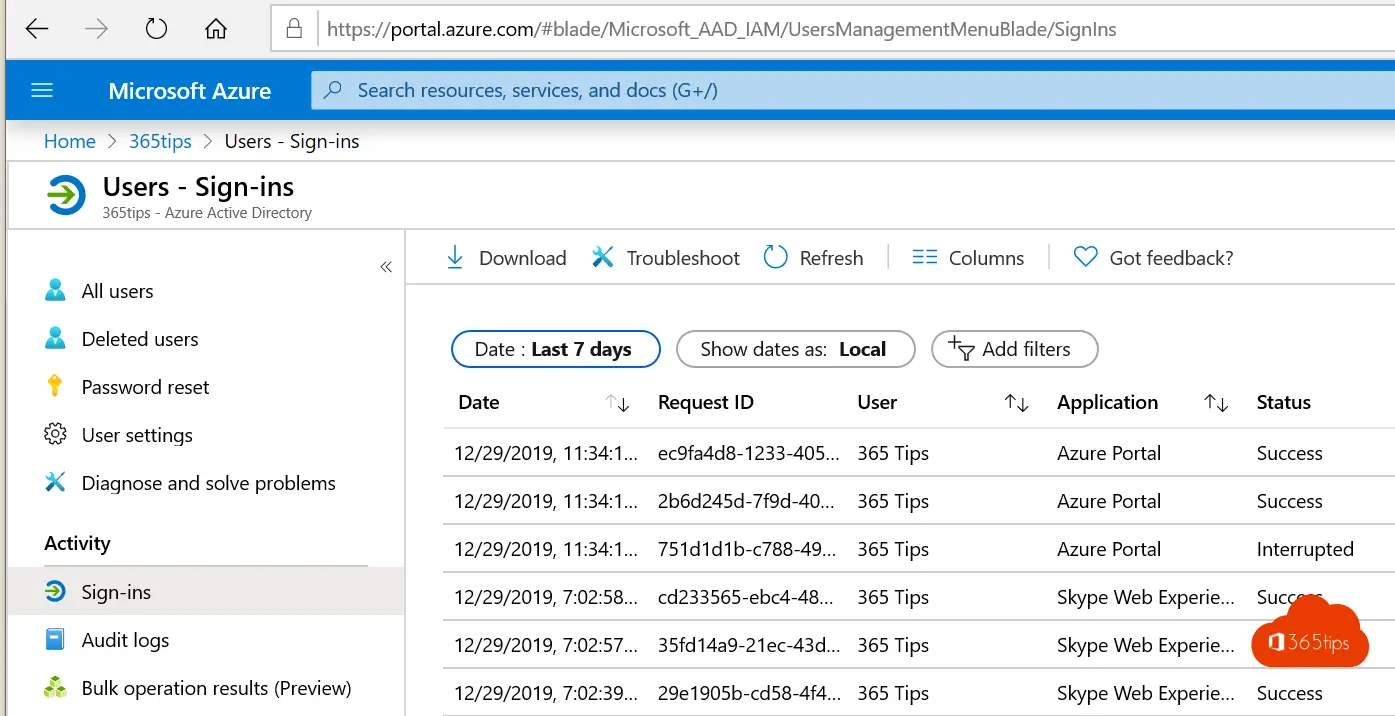
Click Sign-ins to view all login attempts.
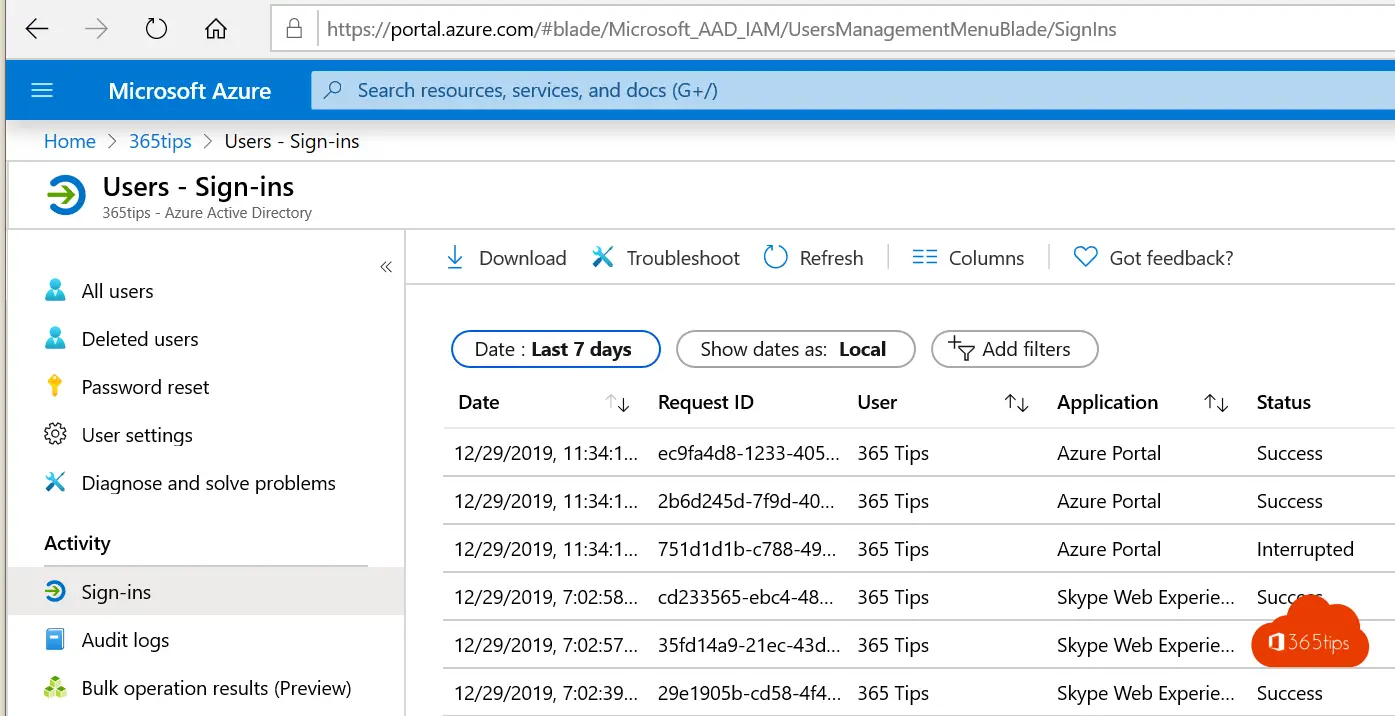
Download the full CSV file.
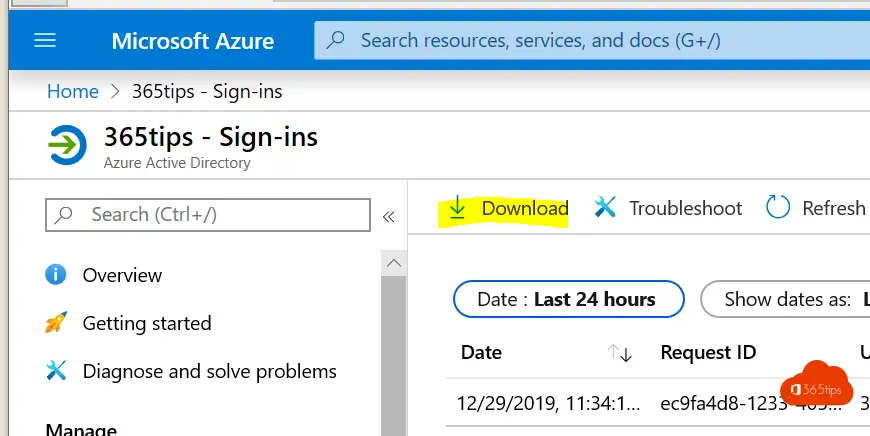
Download the CSV file and filter for example by not a specific location to get insights on risk and successful unwanted login attempts.
Summary
With current data, you are able to understand risks that exist in your environment today that you can act upon. It's often unknowable how many risks there are and how many sign-ins are happening from places we don't have users from.
Is your organization now convinced of the value of Multi-factor authentication?
